This is the second part of my article about deploying Sitecore through Terraform. The first part can be found here and discusses Terraform features and explains why Terraform is a good fit for deploying Sitecore.
This article will walk through my sample Github solution which deploys a Sitecore site in Azure through Terraform. Below graph generated by Terraform’s Graph command shows the components which will be created.

Clone Github Repo
This article uses the code from the Github repo which can be found here. This repo contains a variables.tf file. The first section of this file needs to be populated with settings specific to each deployment. In this article these values will be set in a file called secret.tfvars which is excluded form Github. The variables can be set like below:
StorageKey = "your value"
LicenseFile = "your value"
BacpacCoreDB = "your value"
BacpacMasterDB = "your value"
BacpacWebDB = "your value"
VCppPackage = "your value"
SitecoreZip = "your value"
DomainNameLabel = "your value"
xDbDisableFile = "your value"
The last setting is xDbDisableFile. This patch file disabled xDB as this repo stands up a Sitecore XM topology without xDB. Folllowing is in this file, but it can also be used to patch in other settings.
<configuration xmlns:patch="http://www.sitecore.net/xmlconfig/" xmlns:set="http://www.sitecore.net/xmlconfig/set/" xmlns:role="http://www.sitecore.net/xmlconfig/role/">
<sitecore>
<settings>
<setting name="Xdb.Enabled">
<patch:attribute name="value" value="false" />
</setting>
<setting name="Xdb.Tracking.Enabled">
<patch:attribute name="value" value="false" />
</setting>
</settings>
</sitecore>
</configuration>
After the initial setup this article will follow the standard 4-step Terraform workflow which can be seen below.

Terraform Init
After getting the repo Terraform needs to initialize the working directory and download the Azure Resource Manager provider. Running terraform init will take care of this:

Terraform Plan
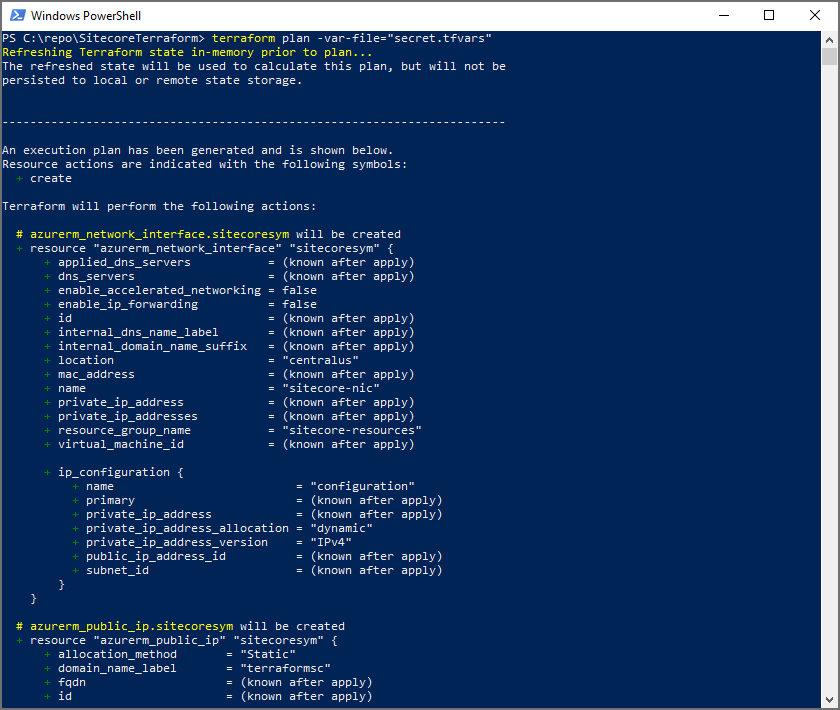
The plan command can be run now that the workspace is initialized. This will show all the resources which will be created, in this case 11 resources will be created:
- Network Interface
- Public IP
- Resource Group
- Sitecore Core Database
- Sitecore Master Database
- Sitecore Web Database
- Firewall rule for SQL traffic
- Azure SQL DB server
- Subnet
- Virtual Machine
- Virtual Network
As mentioned before the values of some of the variables are specified in secret.tfvars, this will be passed into the plan command terraform plan -var-file=”secret.tfvars”. Below is the start of the output from this command:
Terraform Apply
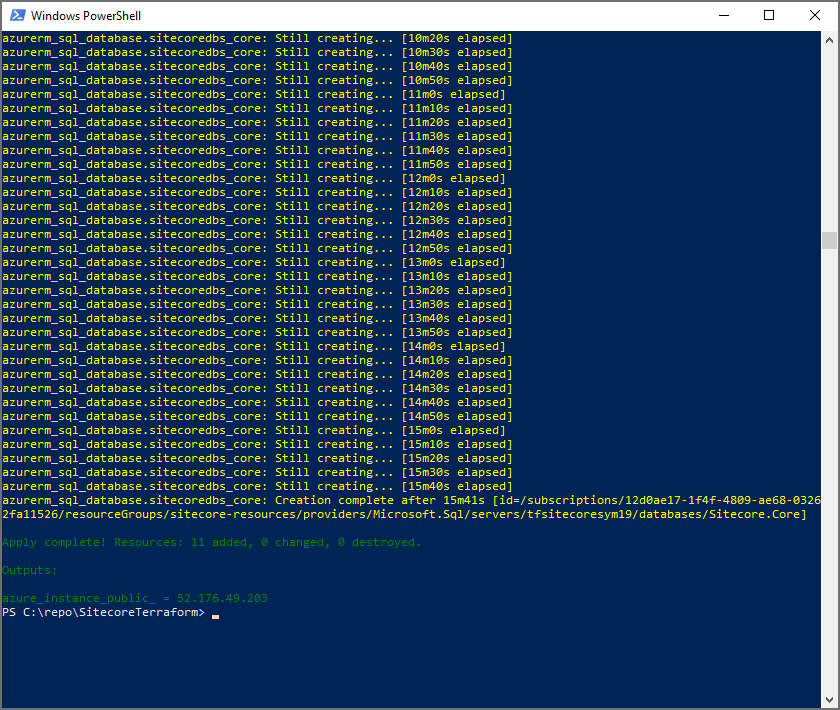
The apply command can be run now after the output from the plan command is reviewed. This will create the 11 resources from the plan command which make up the Sitecore site.
Inside the files folder in the repo is a winrm.ps1 script. This will be put on the virtual machine which is created by Terraform and will setup Sitecore. This file uses some variables which are passed in by the main.tf file here
The apply command will also need the Terraform variables files so the full apply command will look like this: terraform apply -var-file=”secret.tfvars”, this will create the resources and returns a success message after this is done:
The Sitecore site can be opened when this is done and when the winrm.ps1 powershell script is complete. By default it will be publicly accessible at <domain-name-label>.<azure-region>.cloudapp.azure.com, see below for the example with this setup:

Terraform Destroy
When done all resources can be torn down again by running terraform destroy. This is obviously an optional step, however it is important to continue to make any changes to resources through Terraform to ensure the code stays up to date and the deployment process is repeatable, predictable and automated.
